BGP and IS-IS: How Internet Routing Actually Works
I’ve been working with BGP and IS-IS at BelWü for my research assistant position, and honestly these protocols made way more sense once I saw them running on actual production infrastructure instead of just reading RFCs. Here’s what I’ve learned.
BGP: Routing Between Networks
BGP (Border Gateway Protocol) is what makes the internet work. It’s how different networks (called Autonomous Systems) talk to each other and figure out how to route traffic.
The basic idea: every organization that connects to the internet gets an AS number. Universities, ISPs, cloud providers, they all have their own AS. BGP is how these networks tell each other “hey, I can reach these IP addresses, send traffic to me.”
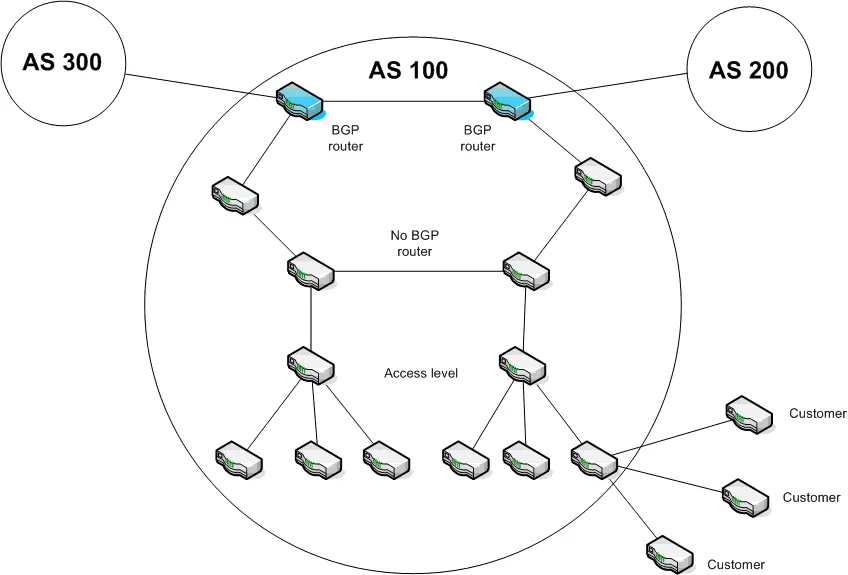
This diagram shows how it’s structured. AS 100 is in the middle (that’s like BelWü). AS 300 and AS 200 are neighboring networks (other universities or ISPs). The blue routers at the edge of AS 100 are running BGP to talk to the outside world. Everything inside is using interior routing protocols.
Why BGP is tricky
BGP doesn’t care about link speed or latency. It picks routes based on policy. This means an AS can prefer a slower path through a specific provider for business reasons, or avoid certain networks entirely.
At BelWü we use BGP to peer with DFN (the German research network) and various internet exchanges. Each connection is a BGP session. We announce which IP prefixes we own, and they announce theirs.
The thing that surprised me: BGP has no built-in authentication. Anyone can announce any prefix. That’s why RPKI (Resource Public Key Infrastructure) exists. I spent a lot of time working on RPKI validation to make sure we only accept legitimate route announcements and don’t get hijacked.
BGP sessions: eBGP vs iBGP
There are two types of BGP sessions:
eBGP (external BGP): between different AS numbers. This is what you use to talk to other networks. The routers at the edge of AS 100 talking to AS 300 and AS 200, that’s eBGP.
iBGP (internal BGP): within the same AS. The BGP routers inside AS 100 need to share routes with each other. That’s iBGP.
The confusing part: iBGP doesn’t automatically redistribute routes. If Router A learns a route via eBGP and tells Router B via iBGP, Router B won’t tell Router C unless you set up a full mesh or use route reflectors. This caught me out when I was debugging why some routes weren’t propagating correctly.
IS-IS: Routing Within Networks
While BGP handles routing between networks, you need something to route within your network. That’s where IS-IS comes in.
IS-IS (Intermediate System to Intermediate System) is a link-state protocol. Every router builds a complete map of the network topology and calculates shortest paths using Dijkstra’s algorithm.
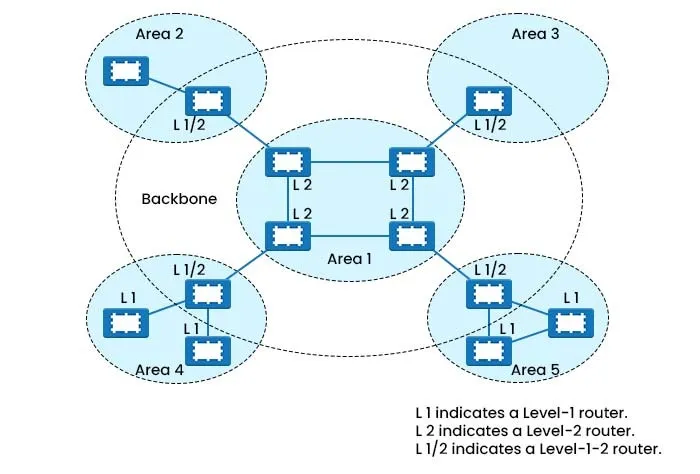
This shows how IS-IS organizes a network into areas. The backbone is in the middle (Area 1). Surrounding areas (2, 3, 4, 5) connect to it. This hierarchy keeps routing tables manageable in large networks.
Level-1 vs Level-2 routers
IS-IS has this concept of router levels:
Level-1 routers: only know about their local area. They route within Area 2, for example, but don’t know the topology of Area 3.
Level-2 routers: know the entire backbone topology and how to reach other areas. They’re like the interstate highway system.
Level-1-2 routers: do both. They route within their area AND participate in backbone routing. These are the routers at area boundaries.
In the diagram, Area 1 is all Level-2 (backbone). Areas 2-5 have Level-1 routers for local routing and Level-1-2 routers to connect to the backbone.
Why this hierarchy matters
Imagine BelWü’s network with hundreds of routers. If every router had to know about every other router, the routing tables would be massive and convergence would be slow.
With IS-IS areas, a router in Area 4 only needs detailed topology for Area 4. For everything else it just knows “send to the nearest Level-2 router.” This scales way better.
When a link fails in Area 4, only Area 4 routers recalculate paths. The backbone doesn’t care about internal Area 4 topology changes unless an area border router goes down.
IS-IS vs OSPF
People always ask why use IS-IS instead of OSPF (the other popular link-state protocol). From what I’ve seen at BelWü:
IS-IS runs directly on Layer 2, not IP. This means it keeps working even if IP addressing gets messed up. Useful for troubleshooting.
IS-IS has cleaner area boundaries. OSPF Area 0 (backbone) has to be contiguous. IS-IS Level-2 can be discontinuous.
IS-IS is more extensible. Adding new features doesn’t break the protocol. This matters for IPv6 and MPLS support.
That said, OSPF is more common in enterprise networks. IS-IS dominates in ISP/carrier networks. BelWü uses IS-IS because we’re essentially running a small ISP for research institutions.
How BGP and IS-IS work together
In a typical setup like AS 100 in the first diagram:
IS-IS handles routing inside the AS. All the internal routers use IS-IS to find each other.
BGP runs on edge routers to exchange routes with external networks.
BGP routes get redistributed into IS-IS so internal routers know how to reach external destinations.
IS-IS routes get redistributed into BGP so external networks know how to reach our internal networks.
The edge BGP routers are usually Level-1-2 routers in IS-IS terms. They participate in the backbone and connect to external BGP peers.
Things that caught me out
BGP timers are slow by default. Hold time is often 180 seconds. If a BGP peer dies, it can take 3 minutes to detect and reroute. You can tune this but aggressive timers can cause instability.
IS-IS circuit types matter. Point-to-point vs broadcast networks behave differently. I spent way too long debugging why IS-IS neighbors weren’t forming before realizing the circuit type was wrong.
Route filtering is critical. You don’t want to accidentally announce your entire internal network to the internet, or accept bogus routes from peers. I learned this by reading BelWü’s routing policies and understanding why every filter exists.
Metric manipulation can break things. IS-IS uses cost-based metrics. If you set a link cost way too high to discourage traffic, you might accidentally make it unusable as a backup path when primary paths fail.
What I’m working on now
At BelWü I’ve been focusing on RPKI deployment. We validate BGP announcements against RPKI records to detect hijacks and misconfigurations. This involved setting up RPKI validators, configuring ROA (Route Origin Authorization) checking on our BGP routers, and writing monitoring scripts to alert on invalid announcements.
I also worked on the FlowPipeline project which processes NetFlow data. Understanding BGP is important there because flow records contain AS numbers, and we use AS path information for threat intelligence correlation.
Why this matters for my thesis
My thesis is on VR robot teleoperation with haptic feedback, which seems completely unrelated to BGP and IS-IS. But the network infrastructure knowledge helped me understand real-time communication requirements.
Low-latency paths matter. BGP might pick a longer AS path with lower latency, or a shorter path with higher latency. For VR teleoperation where I need sub-40ms round trip time, understanding how routing works helps me make architectural decisions.
The ESP32 in my haptic glove sends UDP packets to Apple Vision Pro over WiFi. That traffic might go through multiple network hops. Understanding routing helps me debug when latency spikes or packets get lost.
Learning resources that actually helped
RFC 4271 (BGP-4): dry but comprehensive. Good reference.
RFC 1142 (IS-IS): older but explains the core concepts clearly.
BelWü’s production configs: seeing real router configurations taught me more than any textbook. Policy statements, route maps, area configurations, all the practical stuff.
Wireshark captures of BGP and IS-IS packets: actually seeing the protocol messages helped me understand the exchange sequences.
Final thoughts
BGP and IS-IS are complex because the internet is complex. Thousands of networks with different policies, hardware, and requirements all need to interoperate reliably.
The key insight for me was understanding the separation of concerns. BGP handles policy and inter-network routing. IS-IS handles fast convergence and intra-network routing. Each protocol does one thing well.
If you’re learning this stuff, set up a lab. GNS3 or Containerlab let you run actual router images. Configure BGP sessions between virtual routers. Set up IS-IS areas. Break things and fix them. That’s how it actually sticks.
~Ajit George